Learning that Russian hackers stole more than a billion Internet-user credentials was kind of like losing a bag of underwear on an airplane. It made us very uncomfortable. And obsessed with Las Vegas-based LaunchKey's free mobile authentication app, which doesn’t use passwords or store user information. Co-founder and CEO Geoff Sanders should probably be richer than Mark Zuckerberg. (It’s still a startup, give him a minute.)
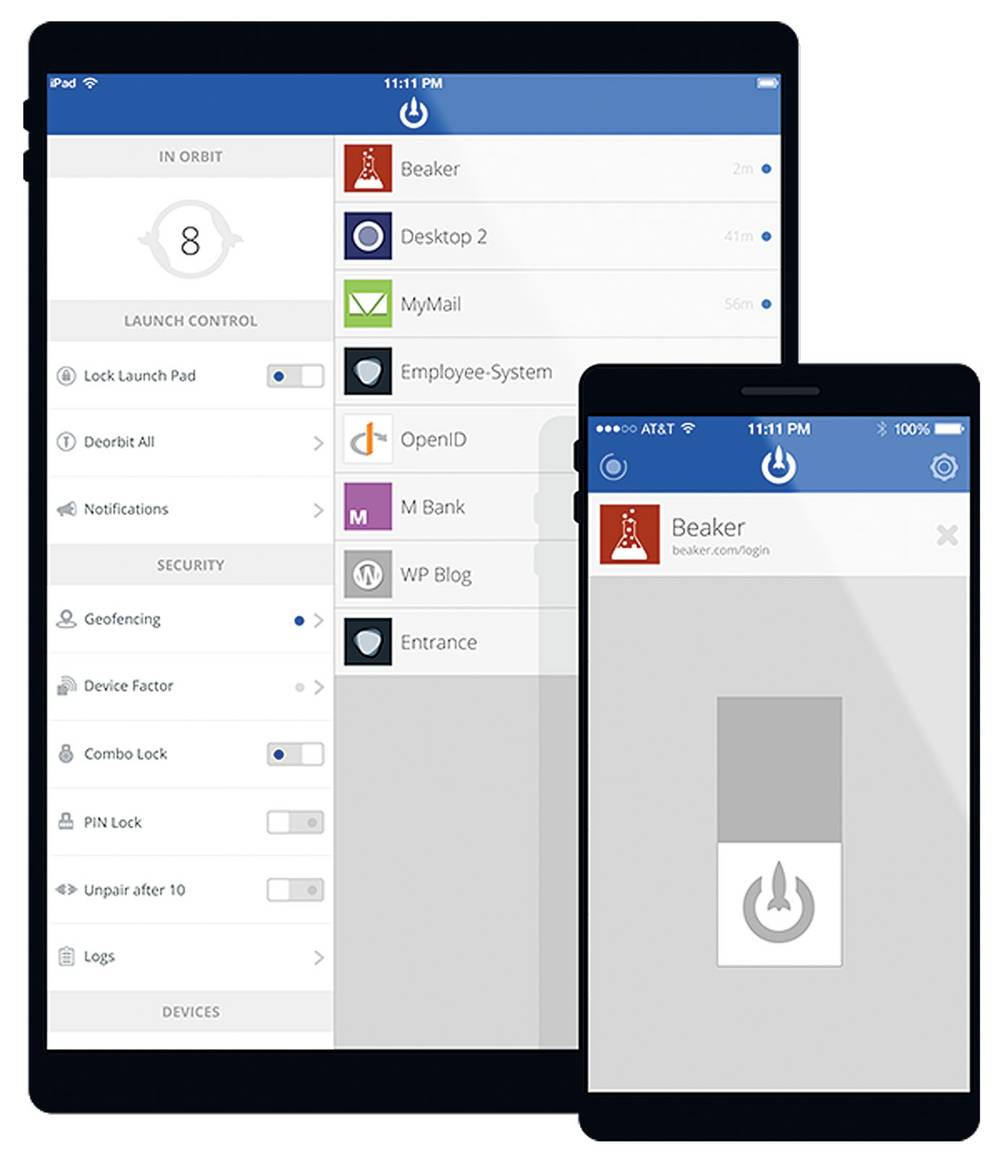
How does LaunchKey address the sign-in scariness? There are optional “auth factors,” from a biometric facial scan to geofencing, but the basic idea is that you enter your username on a LaunchKey-enabled site and the service sends your chosen device a launch request. Swipe to connect, knowing that the sensitive information hackers salivate over never leaves your hand. While LaunchKey develops premium services for the big companies that keep losing our underwear, so to speak, we could already be going commando.
We asked Sanders how scared we should be, and to help us understand how LaunchKey is fighting the good fight.
You must have mixed feelings about massive hacks like this latest one. They hammer the point that passwords suck, yet so many users still depend on them. While some security experts doubt that the Russian hack has any real teeth, how paranoid do you think average users should be? As a company that's been preaching "kill passwords" for many years now, it's bittersweet to see these breaches take place, but it reinforces what we've always said: passwords can't be secure and the problems they cause will only become more severe with time. Massive hacks like the one involving this Russian hacking group absolutely should concern the average user, as it shows just how vulnerable the foundation of security and access control is online today. Hacking password-protected systems is becoming no harder to bypass than your typical door lock; with just a little knowledge and the right tools, virtually anyone can do it.
In the two years since your team won Las Vegas Startup Weekend, how much competition has sprouted up in the market? Is Google the only one of note, or are there others working on services similar to LaunchKey? While we've seen an increase in attention to the password problem since we started over two years ago, virtually all of the solutions that have come to market rely on a two-step authentication approach that doesn't get rid of the password. This is why we consider these solutions temporary bandages rather than cures. While two-step authentication solutions like Google Authenticator do provide more security than passwords alone, LaunchKey is unique in that it can completely remove passwords from the authentication flow. LaunchKey is truly the first ubiquitous authentication platform that shifts login and authentication requests to the mobile devices we all already own.
How many downloads has the app had since it went live (and did numbers jump in the wake of recent news), and what's the status of LaunchKey's development of a monetized high-end version for big organizations? While we don't provide specifics at this time, I can tell you that we have thousands of active users and developers utilizing LaunchKey Mobile and the LaunchKey API, and big password breaches like this do typically raise traffic and interest in our solution. As a security startup dealing with something as critical as authentication, we've taken a steady and measured approach in going to market. While our first 18 months were focused on development and testing, we're currently conducting pilots with multiple clients across many sectors including banking, finance, healthcare, telecommunications, automobiles and beyond. We plan on releasing more details on premium services within the next few months.
Speaking of monetizing, what do you think of Hold Security charging companies for confirmation of whether they've been hacked? Personally, I don't see any problem with Hold Security charging businesses for this type of service. Professional services that provide value to a business typically cost money, and security should be treated no differently. In fact, I'd say it has been businesses' unwillingness to treat cyber security with the attention it deserves that has gotten us so deep in a hole. However, this does highlight an important weakness of the password model: it relies on businesses, developers and other purveyors of passwords to implement and secure them correctly on our behalf.
Given that LaunchKey is still a startup, I'm sure there are many sites that are not yet enabled for the service. Do you have a list you can share? While we don't publicly disclose who uses the LaunchKey service (we leave that up to the discretion of our clients and developers), I can say that we've been conducting pilots with a wide variety of online services and organizations including a handful of Fortune 500 companies. Our pilots and beta testers cover a wide array of sectors, including finance, banking, healthcare, IT, telcos and beyond. With that said, some of our early partners have publicly disclosed partnerships with LaunchKey, including Coinsetter, Rivetz and vehicle manufacturer Local Motors. Additionally, you can log in with LaunchKey anywhere where OpenID is accepted such as the popular Q&A community, StackExchange. We also have free plugins for WordPress and Drupal.
Smartphones can be infiltrated, so isn't personal data always vulnerable, whether or not we have authentication safeguards for signing in to particular sites? Help me understand the layers of risk with mobile devices. Typically, the login form used to log in to a website is located on that same website. The username and password credentials you log in with are also stored by that website, typically in databases along with other personal data. We call this an "in-band" architecture, and it's highly vulnerable to a variety of attacks. One of the things that makes LaunchKey so secure is that it decentralizes authentication and personally identifying information by shifting the layer of authentication out of band to mobile devices. This unique architecture removes most of the common attack vectors, while any data used for authentication is encrypted and stored locally on the mobile device, and not in the cloud on LaunchKey servers where data is more at risk.
I attended Black Hat a couple years ago, and one of the things the White Hats stressed was that hackers would always find ways to get what they want. Are you confident that LaunchKey's model can't ever be compromised? Those White Hats are absolutely correct: it should always be assumed that any secure system can be bypassed. It's because of this that we architected LaunchKey in such a manner that not only can we as a service not authenticate on behalf of a user, but we're an anonymous service that doesn't store any personally identifying information on our users. Any personal data utilized for authentication is stored locally on an end user's mobile device, and not by LaunchKey. This means that if an attacker were to breach our servers, not only would they not be able to correlate any specific data with any specific individual, but they'd never be able to authenticate on behalf of a user even if they could.